Credentials
Credential objects provide a way to make authentication data (such as usernames, passwords, and OAuth authentication details) portable across various mapping execution environments, in a secure way. Credentials are useful in mappings that require basic HTTP authentication or OAuth 2.0 authorization. You can define credentials in MapForce and also in FlowForce Server. If credentials were defined in MapForce, you can optionally deploy them to FlowForce Server, similar to how mappings are deployed.
A credential must have a name and a type; all other details are optional. The name is just an indication to the execution engine (be it MapForce or MapForce Server) that the mapping requires credentials to run. You can choose whether the sensitive information associated with the credential should be stored encrypted inside the mapping, or be supplied only at mapping runtime. If you stored the sensitive information inside the mapping, you can still override it when executing the mapping in a server environment.
You can create Password or OAuth 2.0 credentials. To create a credential, take the steps below:
1.Right-click an empty area on the mapping, and select Open Credentials Manager from the context menu. The Credentials Manager grid appears at the top of the mapping pane.
2.Click ![]() Add. A dialog box appears where you can enter the credential information. (The same dialog box appears when you create or edit the HTTP security settings for a Web service component.)
Add. A dialog box appears where you can enter the credential information. (The same dialog box appears when you create or edit the HTTP security settings for a Web service component.)
3.Enter a credential name.
4.Select a credential type (Password or OAuth 2.0).
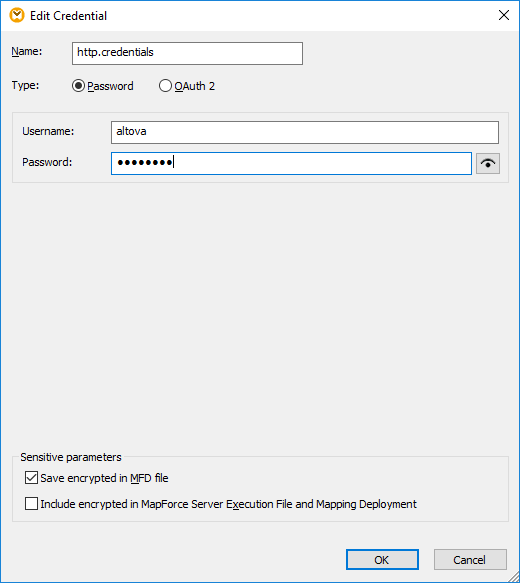
5.To authenticate the mapping at design time, fill in the following fields:
oIn case of "password" credentials, fill in the username and password required to authenticate to the Web service. Confirm the password when prompted to do so.
oFor details concerning OAuth 2.0 credentials, see OAuth 2.0 Credentials.
You may optionally save sensitive data in the mapping design and deploy it to other environments in encrypted form, or not store it at all. If you stored sensitive data, you can still view after closing the mapping, by clicking the Reveal ![]() button.
button.
In case of password credentials, the sensitive field is Password. In case of OAuth 2 credentials, the sensitive fields are Client Secret, Access Token, and Refresh Token. |
The following check boxes let you control the desired behavior with respect to storing sensitive data.
Save encrypted in MFD file | Select this check box to save the sensitive data in the mapping design file (.mfd), in encrypted form. |
Include in MapForce Server Execution File and Mapping Deployment | Select this check box if you would like the sensitive data to be included in the MapForce Server execution file (.mfx) when you compile one as described in Compiling Mappings to MapForce Server Execution Files.
When this check box is selected, the sensitive data will also be included in the package deployed to FlowForce Server, see Deploying Mappings to FlowForce Server. |
The sensitive fields are stored in reversible encrypted form, since they must be decrypted and used at mapping execution time. If you prefer not to store sensitive data, clear the check boxes above. In this case, MapForce may prompt you for the password when you attempt to run the mapping, for example:
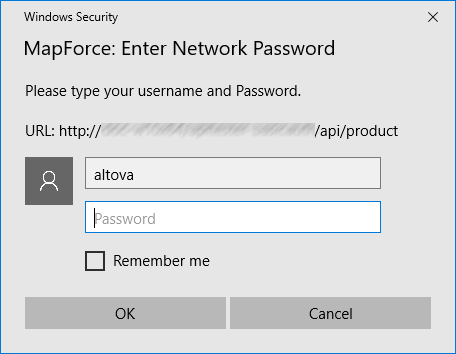
On the server side, you can supply the password dynamically at mapping execution time. For more details, see Credentials in MapForce Server and Credentials in FlowForce Server.